Secrata’s patented technology provides unmatched security at the data layer, flexible deployment, support for existing workflows and easy integration with 3rd party applications and security infrastructure. Secrata’s platform enables secure movement and management of data across devices and storage locations with both internal and external enterprise users.




Secrata’s patented chunking and encryption of data provides multiple layers of security for data at rest and in motion. This triple-layer provides encryption, separation, and authentication. The data is never decrypted or reassembled between the point of origin and the point of destination; whether accessed via the Web Client or Mobile application, your data is never in the clear.

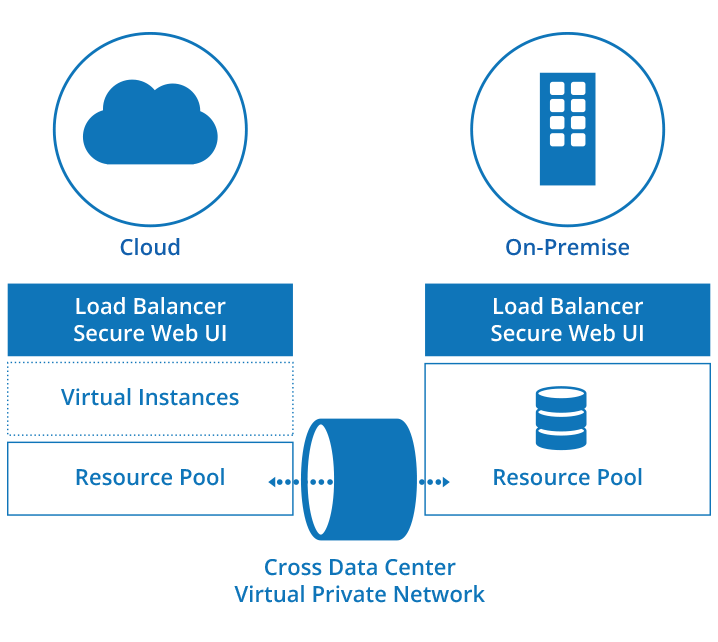
Secrata is cloud agnostic and able to support any cloud infrastructure the enterprise chooses. Secrata ensures that your data is secure at rest and over the wire by providing ownership of the keys regardless of the environment. You own your data no matter where you deploy Secrata! And if you choose to move your data, Secrata is designed to easily change cloud providers. Keeping the enterprise in control and your data secure.

On-premises deployment provides access to files stored on the enterprise network while always ensuring your data is secure. No VPN required, users can easily and securely access their files quickly while on the go. This solution is ideal for the enterprise that chooses to segregate its highly regulated data.
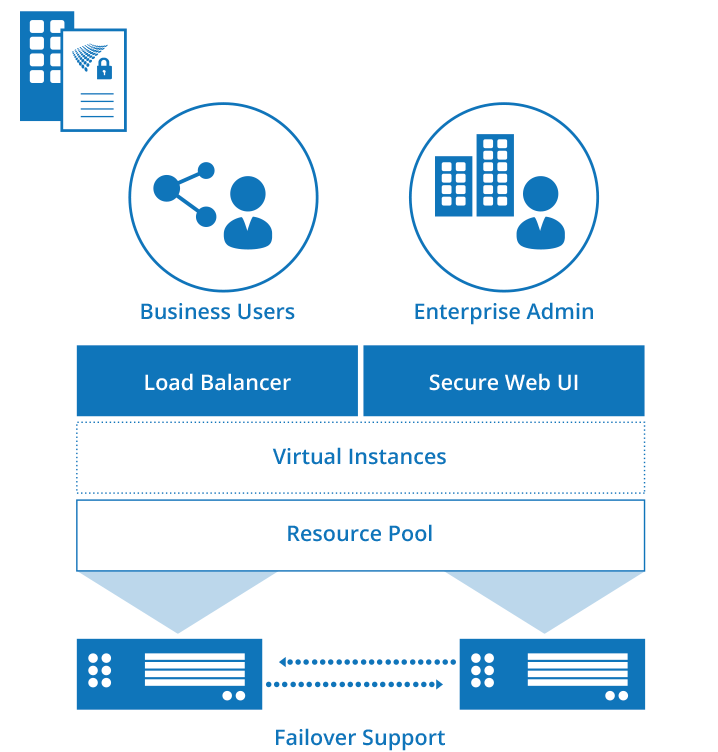

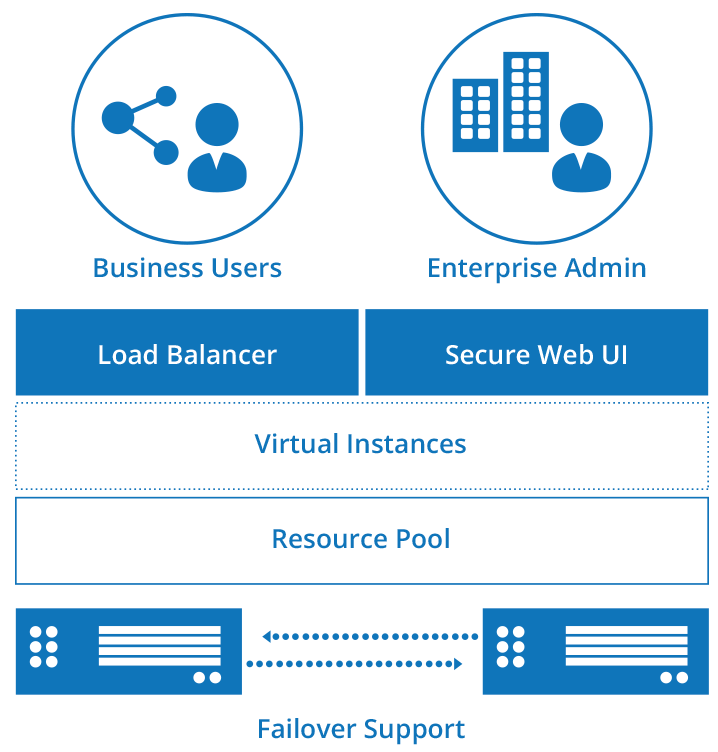
Hybrid solutions can be configured to keep failover support and resource pools within the enterprise network. This ensures that in the event of a network outage the enterprise is able to get the services back up and online without depending on outside resources.